Getting Control of External Sharing in Microsoft 365
How to secure, manage, and control External Sharing in Microsoft 365
A very large number of us will have interacted with External Sharing in Microsoft 365 in our working lives, even if we don’t use Microsoft technologies day to day. You may have shared a file as part of a project, a marketing communications activity or even for supplier management. Equally, you may have been the recipient of an externally shared file, which you could easily access anonymously or by using your own credentials.
However, do organisations really understand how External file Sharing works and how to effectively manage it in order to avoid sensitive information being shared incorrectly?
Understanding External Sharing
External Sharing allows the sharing of a file from OneDrive, SharePoint and Teams with one or more users who are external to the organisation’s Active Directory. A link is created for the file, which dependant on an organisation’s settings, will either require a login to access or can be accessed anonymously by anyone with the link.
The first thing to understand about External Sharing is that it is not the same as guest access for Microsoft Teams. As standard, a guest user can access the content of the Team, including all the files in the SharePoint Site. External file Sharing can be enabled regardless of the guest access settings and allows external users access a specific file via a dedicated link.
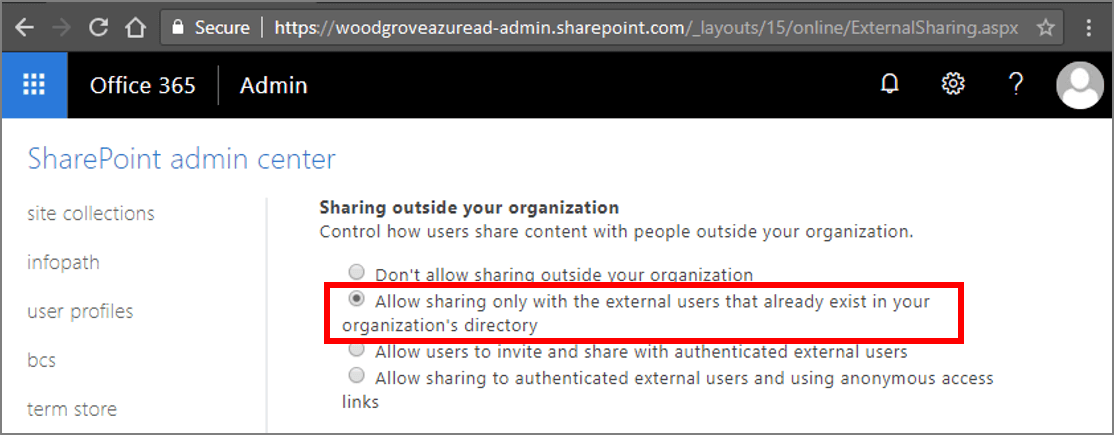
The second thing to understand is that the ability to share files externally is controlled at both the workspace and the tenant level. In the SharePoint Admin Centre, the default External Sharing settings are set for the tenant, with the following options available:
- Only people in your organisation – No external file sharing allowed.
- Existing guests – Only guests already in your organisation’s directory.
- New and existing guests – Guests must sign in or provide a verification code.
- Anyone – Users can share files and folders using links that don’t require sign-in.
Each Site can either inherit the tenant level settings or have specific settings up to the level of the tenant default. It is, therefore, possible for sharing of files to be restricted from certain Sites but allowed in others.
The final thing to understand about External Sharing is how the permissions are granted to a specific document. Permission inheritance is broken and unique permissions are applied to an individual document. This can cause confusion when permissions are modified at the Site level and not reflected on the shared document.
Better Management of External Sharing
External Sharing is a great feature to allow external parties access to an individual document in Microsoft 365. However, if not managed properly, documents can be incorrectly shared and sensitive information put at risk. ProvisionPoint 365 can help organisations introduce greater control without disabling the sharing capability. It does this by applying the correct settings at the point of provisioning, management throughout the lifecycle and ongoing reporting.
ProvisionPoint Workspaces allows organisations to control which Sites and Teams have External Sharing enabled. Each workspace template defines the specific settings which will be set and whether the requestor of a workspace can change that setting. Furthermore, the ongoing governance of External Sharing can be managed using Actions that allow a Site Owner to request a change to the settings as and when required.
ProvisionPoint Permissions allows Site Owners and administrators to report, in one click, where files have been shared externally. The Sharing Link report, which can be run on multiple Sites at once, includes details on each file and who has access. It is also very easy to take immediate action on any incorrectly shared files and remove access without going through multiple complex steps.
If you would like to find out more about ProvisionPoint Workspaces or ProvisionPoint Permissions, simply contact us.
