5 Steps for Successful Microsoft Teams Governance – Step 3: Security
This is the third blog in our series of five articles based on the recent presentation delivered by ProvisionPoint’s CEO, Peter Baddeley, at the South Coast Summit back in October 2021.
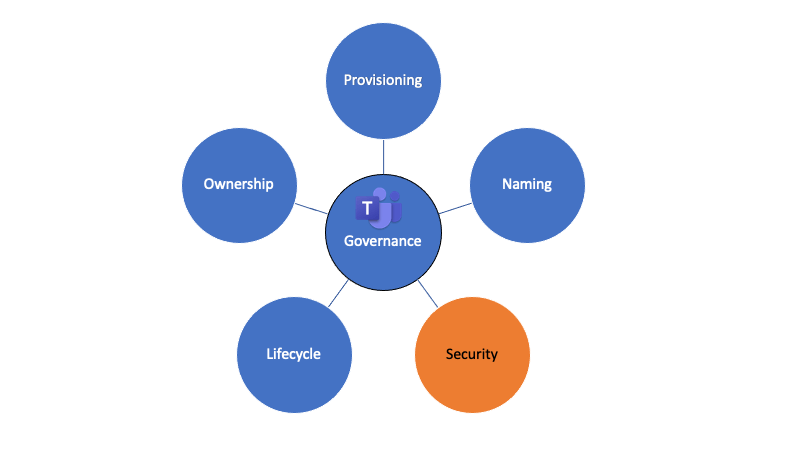
Peter will be looking at five key areas which organisations can address in order to simplify the governance of Microsoft Teams, covering provisioning, naming conventions, security, lifecycles, and ownership. He will also share his first-hand experiences how organisations have successfully implemented Teams governance.
In his third blog, Peter looks at Microsoft Teams Security.
Peter explains:
Who has access to a Team is probably the most frequent issue which organisations bring to us here at ProvisionPoint.
Managing Access to Microsoft Teams
The nature of this concern can vary between organisations – some are more focused on who within the organisation has access, where others are more anxious about who outside the organisation has access. This concern is typically driven by some of the native security setups within Microsoft Teams, for instance, Guest Access is automatically turned on for all Teams.
To best assist organisations, it is important to understand the reasons behind these security concerns. In most cases, they are typically related to managing access to sensitive data and controlling who should and who should not have access. Whether this data is personal, financial or commercially sensitive, many companies are concerned about it being added to a Team and then accidentally shared with the wrong users, both within and outside of the organisation. This is particularly relevant to Teams due to the architecture of Microsoft 365. It is also perhaps the simplest to manage at this level instead of the individual file level.
Security Concerns Do Not Have to Be Complicated
Fortunately, managing these security concerns does not have to be complicated. Organisations first need to be confident that privacy, guest access and external sharing are all correctly applied at the point of provisioning for each Team. We understand that there is some value to sharing some content from certain Teams with external parties, but there must be a middle ground between on or off for all Teams. Secondly, organisations must be confident that these settings continue to remain correct throughout the lifecycle of a Team and non-compliance actioned.
To support the controls outlined above, we recommend that organisations invest in user education to help them better understand the different security settings within Teams and exactly what they mean. It is also worth making it really clear to users what settings are applied to a Team, for example, indicating in a Team name that it is externally shared.
This is the third of the five governance steps for Microsoft Teams. When considering security, it is important to understand the specific areas of concern for an organisation and how best to manage them. Flexible but consistent security policies regarding how these settings are applied should be supported with clear communication to users. In the next post, we will be considering the importance of Teams lifecycle in delivering effective governance.
In the meantime, if you would like to learn more Provisioning, click here or simply contact us.
